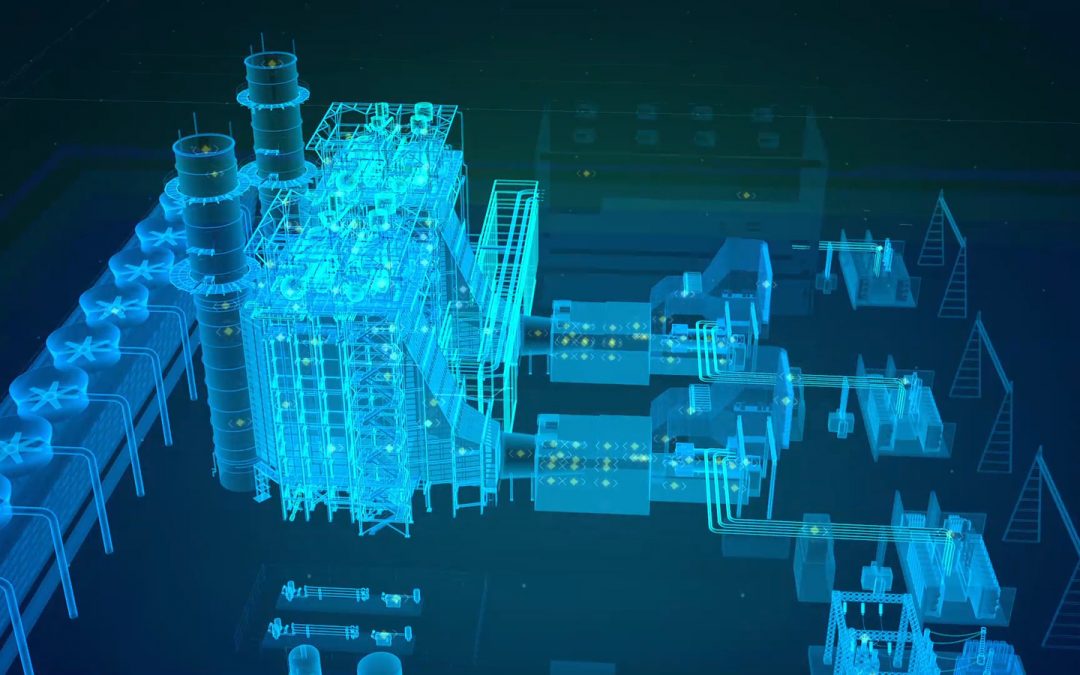
Digital Transformation for Power Plant
Picture by Timothy Cheng Fun, GE Reports. Power system equipment condition monitoring is a must if you wish to ensure the efficiency and reliability of electricity supply. This is typically achieved with equipment maintenance or replacement based on typical service...

How Machine Learning Makes IoT Relevant
Many of the manufacturers involved in developing IoT technology are still finding a way through the evolving landscape. Most, however, remain focussed on convenience. Convenience products won’t sell in significant quantities, however. Instead IoT devices that are...

Where Are People Going With Machine Learning In 2017
Machine learning is an industry in flux. It is not a new industry, but new players are taking the field hoping to make a big impact, sometimes without anything tangible to base that hope on. Many will fail but the result is likely to be a more coherent approach to...
Measuring IT Security
Data breaches seem to have been constantly in the headlines in recent years. This has caused many top level executives to ask this question of their information security officers: “How safe is our data?” In the rapidly evolving world of cloud computing and data...
Behavioral Analysis to Thwart Data Breaches
The idea of a layered approach to security is not new, nor is it revolutionary. Just like with old-time castles and modern-day prisons, security on the internet is a multi-layered and multifaceted tool. However, unlike the physical moats, drawbridges, walls and gates...
Cloud Security in the Gulf
Increasingly, the Middle East is adopting cloud computing and this is creating new challenges in security. Security needs are being handled with new and innovative risk management protocols. In the aviation industry in particular, there has been a key challenge in...
Social Medial Safeguarding
Social media in the 21st century is ubiquitous. However, its soaring and expanding use is causing a headache for IT security professionals who have to contend with a whole new range of problems caused by people's use of social media sites. Greg Masters writes in SC...
Mobilizing Business Intelligence
With every other aspect of the online world moving increasingly onto mobile devices, it is time for the world of business intelligence and analytics to catch up. Mobile BI – with good management, and the right infrastructure – can be a powerful extension for the...
Detecting Unauthorized Access
The world of IT is driving automation and improving service delivery all the time. This is having a direct and positive effect on company revenues as well. It is entirely unfortunate that some of this has being eaten up by the ever more complex ways that criminals and...
China Great Cannon
The internet is now a hostile place - that is the finding of recent research into a cyber-attack on Github. Specifically, the researchers said the entire Chinese internet is now hostile. They say this because they have discovered a tool they have dubbed the Great...
Visualizing data the advanced way
All the rage right now in big data and analytics is advanced visualizations. These are fast-becoming coveted features in the growing market for maps and charts and other new and innovative ways of visualizing and processing all that data. Within the last year, almost...
Social Media a Hackers Dream
Social media, and its ever-increasing use, seems to be fuelling a growing wave of cyber-crime that's linked to its easily exploitable attack surface. Steve Ragan, writing for CSO Online, talks about one very interesting attack surface that criminals have been...